Previously WikiLeaks discovered that iOS vulnerabilities can be used by CIA for monitoring. WikiLeaks threatened Apple that if they doesn’t fix this problem, there will be consequences. Before any responses came from Apple, we learned new reveals already – according to WikiLeaks, not only iOS, but also macOS, which has the vulnerabilities that can be used by CIA.

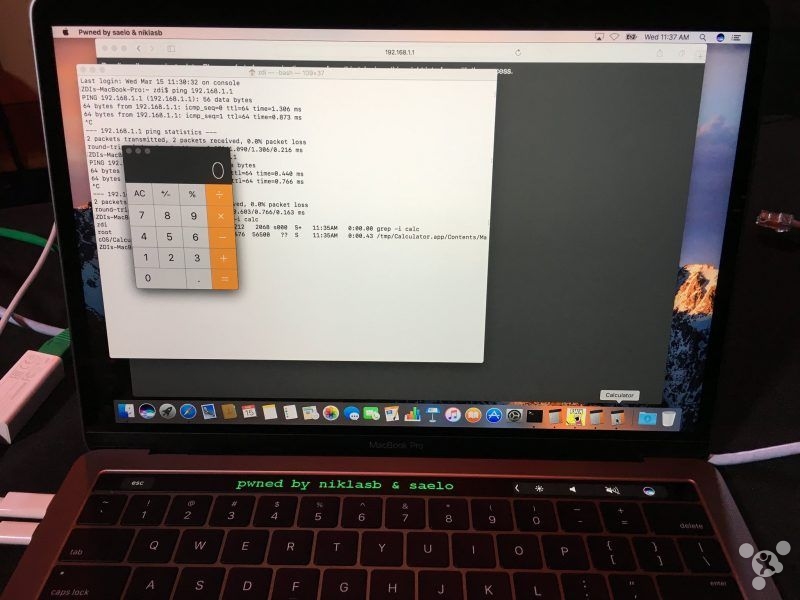
Compared to iOS, macOS seems to be less risky though. WikiLeaks pointed out that CIA mainly uses Thunderbolt EFI vulnerabilities in Mac apps, and reboot won’t make them gone. WikiLeaks, however, also found out during tests that reinstalling the system will block the vulnerabilities, meaning hardware update will permanently fix them until the next infection.
When WikiLeaks newly exposed the problem, Apple has responded that more than 80% of the vulnerabilities were fixed through the latest update, and their engineers had been working on fixing the rest. For that, Julian Assange, founder of WikiLeaks, said they would like to work with Apple, providing information of the vulnerabilities they discover, so that Apple can resolve them with much higher efficiency.